Hiring cybersecurity engineers in 2026 is a challenge, but it’s not impossible. With a global talent gap of 4.8 million and U.S. organizations struggling to fill over 500,000 roles, finding the right talent requires targeted strategies. Here’s what you need to know:
- Key Roles: Security Engineers, Penetration Testers, SOC Analysts, and AppSec Engineers. Salaries range from $70,000 to $165,000+ depending on skills and experience.
- Challenges: Long hiring times (3–6 months), advanced deepfake threats during interviews, and competition from defense contractors offering higher pay.
- Where to Find Talent: Niche communities like CTF platforms (HackTheBox, TryHackMe), bug bounty sites (HackerOne, Bugcrowd), and security conferences (Black Hat, DEF CON).
- How to Assess Candidates: Focus on practical, hands-on tasks like incident response simulations or system hardening exercises. Skip generic coding challenges.
- Retention Tips: Offer certifications, clear career paths, and flexible work arrangements. Build trust and support ongoing learning to keep employees engaged.
With salaries rising 7–10% annually and 88% of companies reporting security incidents due to skills gaps, closing roles quickly and effectively is critical. Below, we’ll explore how to find, assess, and retain top cybersecurity talent.
Cybersecurity Role Types: Matching Skills to Your Needs
::: @figure 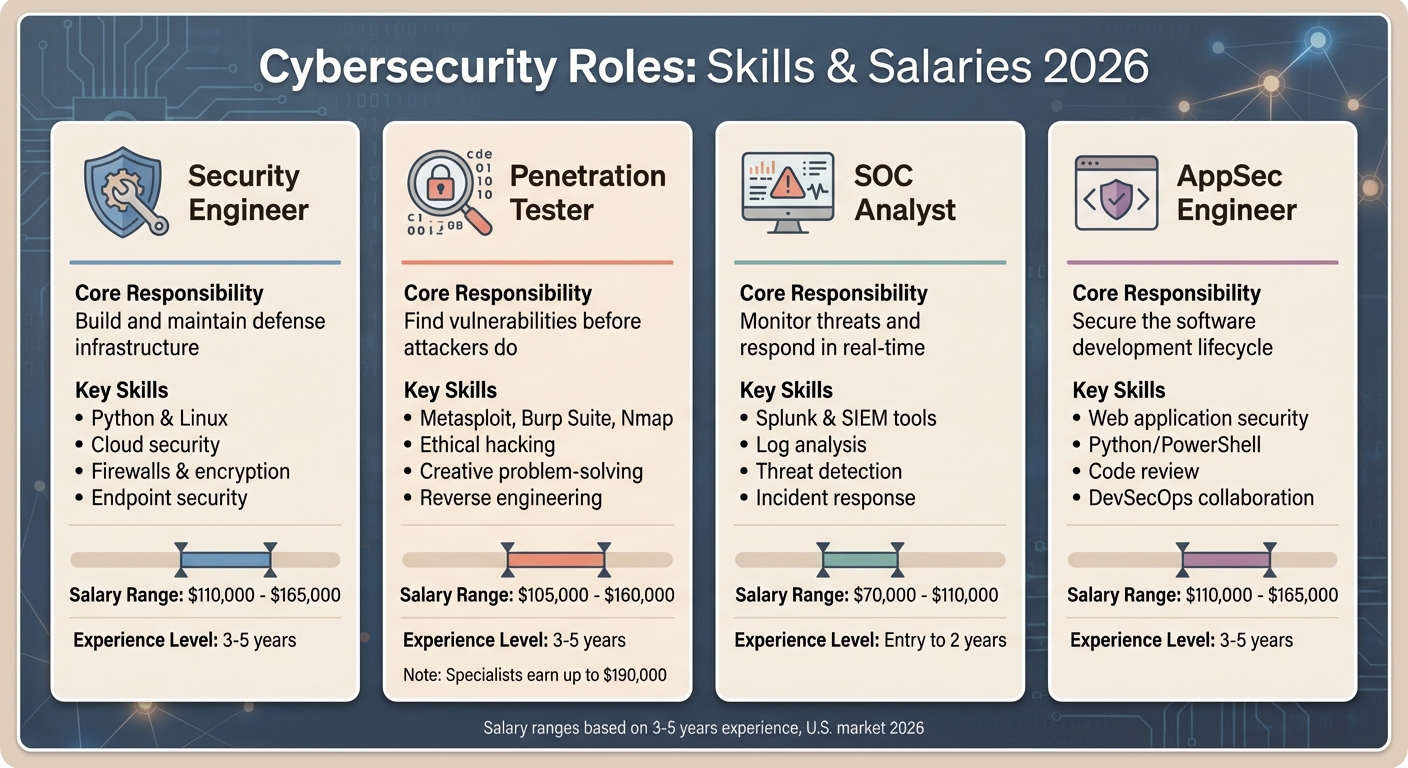 {Cybersecurity Roles: Responsibilities and Salary Ranges 2026}
{Cybersecurity Roles: Responsibilities and Salary Ranges 2026}
Finding the right security professional can make or break your organization's defense strategy. To hire effectively, it's crucial to understand the specific responsibilities and expertise each role brings to the table.
Security Engineer: Building and Maintaining Defenses
Think of Security Engineers as the architects of your cybersecurity infrastructure. They design, implement, and manage critical systems like firewalls, authentication protocols, encryption methods, and endpoint security tools . If you're scaling your cloud infrastructure or need a secure network from scratch, this role should be at the top of your list.
These professionals need a strong foundation in coding with languages like Python and Linux, along with expertise in cloud security . Their work ensures your systems remain protected day in and day out. Salaries for Security Engineers with 3 to 5 years of experience typically range from $110,000 to $165,000 .
Now, let’s shift focus to roles that test your defenses to uncover weaknesses.
Penetration Tester: Finding Vulnerabilities Before Attackers Do
Penetration testers, also known as ethical hackers, approach your systems with the mindset of an attacker. Their mission? To identify vulnerabilities before malicious actors can exploit them . By using tools like Metasploit, Burp Suite, and Nmap, combined with creativity and problem-solving skills, they uncover weaknesses that automated tools often miss .
"The best pen testers think like actual attackers, which can challenge conventional interview processes." - Tom Kenaley, Senior Partner and President, KORE1
If compliance or validating your security measures is a priority, hiring a penetration tester - either on a contract or project basis - could be the way to go. Salaries for experienced testers range from $105,000 to $160,000, with specialists in reverse engineering earning upwards of $190,000 .
From proactive testing, let's explore roles focused on continuous monitoring.
SOC Analyst: Real-Time Threat Monitoring and Response
SOC (Security Operations Center) Analysts are your first responders in the fight against cyber threats. They use tools like Splunk to monitor networks, analyze logs, and investigate suspicious activity in real time . Their work is critical in identifying and neutralizing threats as they emerge.
Entry-level SOC Analysts with up to two years of experience can expect salaries between $70,000 and $110,000 . More experienced Tier 3 analysts, who actively hunt for threats rather than just responding to alerts, command even higher pay. These positions require sharp analytical skills, a calm demeanor under pressure, and a keen eye for detail .
Application Security Engineer: Protecting the Software Development Lifecycle
Application Security (AppSec) Engineers focus on embedding security into every phase of software development. From reviewing code to deployment, they ensure that applications are secure from the inside out . Key skills include expertise in web application security, scripting languages like Python or PowerShell, and collaboration with development teams .
If your organization develops software products or has a large development team, AppSec Engineers are essential. They help developers write secure code from the outset, reducing the need for costly fixes later. Salaries for this role are similar to those of Security Engineers, ranging from $110,000 to $165,000, depending on experience .
By clearly defining these roles, you can fine-tune your hiring strategy to bring in the expertise your organization needs.
| Role | Core Responsibility | Salary Range (3-5 years) |
|---|---|---|
| Security Engineer | Build and maintain defense infrastructure | $110,000 – $165,000 |
| Penetration Tester | Find vulnerabilities before attackers do | $105,000 – $160,000 |
| SOC Analyst | Monitor threats and respond in real time | $70,000 – $110,000 |
| AppSec Engineer | Secure the software development lifecycle | $110,000 – $165,000 |
Why Traditional Recruiting Doesn't Work for Security Professionals
Recruiting for cybersecurity engineers is a whole different ballgame compared to general tech roles. The challenges extend well beyond the typical talent shortage and are deeply tied to the unique demands of security work. One of the biggest hurdles? Ensuring that candidates are genuinely who they claim to be - because these hires will have access to critical systems and infrastructure.
"The technical finding without the communication to back it up just sits in a report nobody reads" .
Before diving into technical qualifications, recruiters must first confirm a candidate's identity. This has become increasingly complex. By 2026, deepfake technology has advanced to the point where real-time impersonation during video interviews is a genuine threat. Traditional video calls are no longer enough. Instead, organizations rely on multi-channel verification processes, including cutting-edge biometric tools that analyze blood flow patterns, to ensure authenticity .
Then there’s the added layer of security clearances, which complicates everything. If the role requires government clearance, you're not just competing with tech startups or big-name companies - you’re up against defense contractors. These contractors often pay $20,000 to $40,000 more annually for the same skills and move faster to secure candidates . Plus, cleared professionals aren’t browsing LinkedIn or job boards. They’re typically found through long-standing relationships and specialized networks, making mainstream recruiting methods almost useless .
Speed is another critical factor. While the typical hiring timeline in tech ranges from three to six months, cybersecurity professionals often have multiple offers and expect decisions within three to four weeks . Delays don’t just mean losing top candidates - they increase your organization's vulnerability. With 88% of companies already reporting security incidents linked to skills shortages , every extra week without the right hire adds to your risk exposure. In cybersecurity recruiting, time isn’t just money - it’s security.
Where to Find InfoSec Talent: Sourcing Channels That Work
If you're looking for top-notch security professionals, you won't find them through traditional hiring channels. Instead, they're active in niche communities - competitions, bug bounty platforms, and conferences - where they showcase their expertise. Here's how to tap into these key sources.
CTF Communities: Spotting Competitive Problem-Solvers
Capture the Flag (CTF) competitions are a goldmine for identifying skilled security engineers. Platforms like HackTheBox and TryHackMe host challenges in areas like cryptography, reverse engineering, network security, and web application security. By checking CTF leaderboards, you can quickly pinpoint individuals who excel at solving complex problems under pressure, saving time compared to traditional screening.
"CTF competitions bridge the gap between cybersecurity talents and recruiters by offering a practical and standardized assessment method, evaluating critical skills like problem-solving, collaboration, time management, and pressure handling." - CyberTalents
Hosting your own CTF event can be even more effective. You get a firsthand look at how candidates approach problems, work with others, and manage deadlines - insights that traditional interviews often fail to provide . Similarly, bug bounty platforms offer another venue to identify proven talent with real-world experience.
Bug Bounty Platforms: Finding Security Researchers With a Track Record
Platforms like HackerOne and Bugcrowd connect you with security researchers who have already demonstrated their abilities. By reviewing leaderboards and disclosure histories, you can identify individuals who excel in practical, hands-on security challenges. This approach ensures you're recruiting talent with a proven history of solving real-world problems.
Security Conferences: Networking With Practitioners
Events such as Black Hat, DEF CON, and BSides are perfect for meeting active security professionals. These conferences aren't just about collecting business cards - they're an opportunity to engage in meaningful technical discussions. Ask attendees about the challenges they're working on and show genuine interest in their expertise. Building these relationships can lead to valuable hiring opportunities down the line. These events also complement direct recruiting efforts by helping you establish deeper connections with potential candidates.
daily.dev Recruiter: Reaching Pre-Qualified Security Engineers
Cold outreach rarely works for security engineers, but daily.dev Recruiter offers a better way. This platform connects you with verified security professionals through warm, double opt-in introductions. Built on daily.dev's active community - where developers engage with technical content - it helps you reach passive candidates who aren't actively job hunting but are open to the right opportunity.
Using pre-qualified candidates can significantly reduce hiring timelines. Instead of waiting three to six months , you could secure the right hire in three to four weeks . With 88% of organizations reporting major security incidents due to skills gaps , speeding up the hiring process is essential to strengthening your security posture.
Up next, we’ll explore how to effectively assess the technical skills of these candidates.
Technical Assessment: What to Test and What to Skip
After finding promising candidates from niche communities, the next step is testing their skills in conditions that reflect real-world challenges. Traditional assessments often miss the mark by focusing on irrelevant skills, which can discourage qualified applicants. Instead, concentrate on practical security tasks that align with the actual responsibilities of the role.
What to Test: Practical Security Skills
The best assessments mimic real-world security operations. Skip theoretical questions and dive into hands-on exercises using sandboxed environments. For instance, a Security Engineer might be tasked with hardening a Linux server based on specific security requirements, while a Cloud Security Engineer could work on fixing an environment where IAM credentials were accidentally exposed in a public repository .
Incident response simulations are another great way to evaluate candidates. For example, present a scenario involving a compromised production database and ask the candidate to outline their first five steps, including who they’d notify . This not only tests technical skills but also evaluates how they handle pressure and make decisions in uncertain situations. As Tom Kenaley from KORE1 puts it:
"Technical skills get them in the door but communication keeps them in the role" .
Here’s how you can tailor assessments for specific roles:
| Role | Skills to Test | Real-World Simulation |
|---|---|---|
| Security Analyst | Log analysis, SIEM tools, threat triage | Analyze a log file showing unusual outbound traffic and identify indicators of compromise |
| Security Engineer | Firewall/IDS setup, encryption, system hardening | Harden a Linux server based on specific security guidelines |
| Cloud Security Engineer | IAM roles, container security, cloud misconfigurations | Fix an environment where IAM credentials were exposed in a public repository |
| Penetration Tester | Vulnerability discovery, exploit analysis, reporting | Identify and document web app vulnerabilities, including their business impact |
Make sure your assessment includes a component where candidates explain their technical findings in plain language for non-technical stakeholders. With 88% of organizations reporting security incidents linked to skills gaps , the ability to communicate risks in business terms is just as important as technical expertise.
Focus on these real-world scenarios to assess candidates’ practical skills while avoiding generic or irrelevant tasks.
What to Avoid: Standard Coding Challenges
Generic coding tests, like those focused on algorithmic efficiency or data structures, don’t measure the expertise needed for security roles. These challenges often reward quick answers rather than the detailed analysis essential for security work . For example, a penetration tester specializing in infrastructure security doesn’t need to know how to optimize sorting algorithms - they need to find vulnerabilities before attackers do.
Avoid testing candidates on technologies they won’t use in their role. Also, steer clear of overly long assessments that prioritize speed over quality or depth . Unrealistic expectations, like requiring 10+ years of experience in technologies that have only existed for five years, can also discourage talented applicants .
"The best technical assessments feel less like an interrogation and more like a collaborative problem-solving session. You want to see how a candidate thinks, not just what they know." - TekRecruiter
Design your assessment as a collaborative exercise rather than a grilling session. This approach helps you understand how candidates approach challenges and whether they can clearly explain their reasoning. No matter the outcome, provide constructive feedback to show respect for the candidate's time and maintain a strong employer brand .
Hiring engineers?
Connect with developers where they actually hang out. No cold outreach, just real conversations.
Compensation Expectations: Security Engineer Salary Benchmarks
Cybersecurity professionals are among the highest-paid in the tech industry, with an average salary of $135,969 across the United States . This figure reflects a 7% premium over general software engineering roles, which average around $127,000 . The higher pay highlights the importance of security roles, especially given the ongoing talent shortage in the field . As Tom Kenaley, Senior Partner and President at KORE1, explains:
"Cybersecurity compensation moves 7 to 10 percent per year depending on the role."
Salaries in this field vary based on experience and specialization. Entry-level roles typically fall between $62,000 and $90,000, while mid-level positions (3–5 years of experience) range from $90,000 to $148,000 . Senior engineers with 6–10 years of experience can expect $120,000 to $200,000, and those in principal-level positions may earn up to $260,000 in base salary . Specializations also play a role in compensation: Cloud Security professionals earn 15–25% more, and those in AI Security see premiums of 15–40% .
Certifications are another key factor in boosting pay. For example, CISSP certification holders earn $25,000 to $35,000 more annually compared to their uncertified counterparts. Similarly, holding an active Top Secret security clearance adds an extra $15,000 to $30,000 to base salaries . Location also significantly impacts pay. San Jose leads with an average annual salary of $175,520, followed by San Francisco at $168,160 . However, employers often reduce salaries by 10–20% in areas with lower living costs .
Beyond base pay, compensation packages often include equity, performance bonuses, and training budgets. For instance, SANS training courses, which can cost between $7,000 and $9,000, are frequently covered by employers . With 53% of employers increasing starting pay to address the talent gap , candidates have strong leverage to negotiate comprehensive compensation packages that go beyond just base salaries. These insights can help recruiters and candidates navigate the competitive landscape of cybersecurity hiring.
Building a Security Team Culture That Retains Talent
Hiring cybersecurity professionals is just the beginning - keeping them engaged and motivated takes intentional effort. 78% of cybersecurity professionals say their team is a key factor in job satisfaction, while 73% credit their manager as a primary reason for staying in a role . With retention rates dropping from 75% in the first year to 66% by the second , organizations need to address burnout, career progression, and trust right from the start. A strong internal culture not only keeps your team intact but also strengthens your overall security posture and reduces vulnerabilities. Here's how to create a culture that attracts and retains top talent.
Respect Privacy and Build Trust
Cybersecurity professionals are acutely aware of data privacy, so how you handle their information during the hiring process matters. Avoid using personal details from social platforms in unsolicited messages - this shows respect for their privacy and sets a positive tone. Once they join, grant them autonomy in decision-making and ensure they have the tools they need without unnecessary bureaucratic hurdles. Empowering your team to respond swiftly to threats isn't just about fostering trust - it's also a smart business move.
Support Certifications and Ongoing Learning
Investing in certifications like CISSP, CISM, and CEH is a must. CISSP-certified professionals often earn higher salaries , and 65% of cybersecurity roles now require ongoing certification updates . Beyond funding certifications, allocate 10% to 15% of work hours for activities like research, threat hunting, or contributing to open-source projects . As TekRecruiter emphasizes:
"A cybersecurity professional's greatest asset is their knowledge. An offer that invests in their continuous education is an offer that invests in the company's long-term security."
Make professional development a core part of their job. Use dedicated budgets - 75% of hiring managers already have one - to cover conference attendance at events like Black Hat or DEF CON. Scheduling study time during work hours can also help prevent burnout. These efforts not only enhance individual skills but also create a culture of shared growth and development.
Create Opportunities for Collaboration and Growth
Lay out clear career paths, whether it's advancing from SOC Analyst to Security Architect or pursuing leadership roles like CISO. Offer both technical and management tracks to suit different aspirations. Pair new team members with mentors and rotate roles to deepen institutional knowledge . With 48% of security professionals feeling overwhelmed by the pace of new threats , it's crucial to balance workloads and celebrate achievements - whether it's stopping an attack or earning a certification - to boost morale . As Tom Kenaley, President of KORE1, explains:
"The companies that handle [burnout] well keep their people. The companies that don't keep calling us to backfill the same positions at higher and higher salaries."
Encourage team members to participate in speaking engagements or technical blogging to enhance their visibility and position your team as leaders in the field . Flexible working arrangements can also help accommodate diverse needs, further strengthening team loyalty .
Conclusion
Hiring cybersecurity engineers in 2026 demands a fresh and targeted approach. With a staggering 4.8 million unfilled positions worldwide and the workforce gap expanding nearly 190 times faster than the overall job market , traditional job boards are falling short. Instead, tap into niche communities where cybersecurity professionals actively engage. Platforms like r/netsec, specialized Discord servers, and GitHub offer direct access to passive candidates who might not be reachable through mainstream platforms like LinkedIn .
Your hiring strategy also hinges on an effective technical assessment process. Filling roles without addressing skill gaps leaves organizations vulnerable - 88% have reported security incidents linked to these deficiencies . Move away from generic coding tests and focus on practical, hands-on challenges, such as lab exercises and real-world scenarios. For incident response roles, evaluate candidates on their ability to maintain composure under pressure. Leading companies streamline their hiring process, closing roles in 3 to 4 weeks, while the industry average stretches to 3 to 6 months . A faster process not only reduces time-to-hire but also helps you stay competitive with compensation.
Speaking of compensation, cybersecurity roles continue to demand higher pay. Salaries in this field are increasing by 7% to 10% annually, with AI/ML specialists commanding a premium of 30% to 40% . Competitive pay is essential, but it’s only part of the equation.
Retaining talent is just as critical as hiring it. While 75% of security professionals stay with a company for at least one year, that number drops to 66% by the second year . What keeps employees satisfied? According to data, strong teams (78%) and effective management (73%) outweigh compensation or brand prestige . To retain top performers, focus on professional growth: fund certifications, dedicate 10% to 15% of work hours to research and learning, and offer clear career paths with opportunities for both technical advancement and leadership. As Tom Kenaley, Senior Partner and President of KORE1, aptly notes:
"The companies that handle [burnout] well keep their people. The companies that don't keep calling us to backfill the same positions at higher and higher salaries" .
FAQs
How do I choose between a Security Engineer, SOC Analyst, Pen Tester, or AppSec Engineer?
Choosing the right role depends on what your organization needs most:
- Security Engineers: These professionals focus on designing and maintaining security systems to ensure your infrastructure stays resilient against potential threats.
- SOC Analysts: They keep an eye on threats in real time, actively monitoring and responding to incidents as they occur.
- Pen Testers: By simulating attacks, Pen Testers identify vulnerabilities, making them key players in offensive security strategies.
- AppSec Engineers: Their job is to secure applications by integrating security into coding practices and the development pipeline.
Each role addresses a different priority, so align your choice with your specific goals.
How can I verify a candidate’s identity in video interviews in 2026?
In 2026, safeguarding the hiring process during video interviews requires consent-based identity checks to tackle modern threats like deepfakes, AI-driven impersonations, and proxy interview scenarios. Implementing real-time identity verification ensures that the individual on camera is indeed the applicant.
To strike the right balance between security and a smooth candidate experience, consider systems that adjust their strictness based on specific risk indicators. This approach is especially critical in remote hiring, where credentials are more susceptible to tampering.
What’s the fastest way to assess real security skills without generic coding tests?
The fastest way to assess security skills is by using practical, scenario-based tests that mimic real-life cyber incidents. These simulations highlight how candidates tackle challenges, emphasizing their hands-on expertise and ability to solve problems. This method provides a clearer picture of their abilities compared to just reviewing resumes or conducting generic coding assessments.


.png)