The demand for cybersecurity professionals is skyrocketing, with 4.8 million unfilled positions globally and a workforce that needs to grow by 87% to meet current needs. Companies with understaffed security teams face $1.76 million higher data breach costs, and 88% of organizations report incidents tied to skill shortages. Traditional hiring methods aren't working, as top talent often avoids job boards and passive recruitment approaches.
Key takeaways for finding and hiring cybersecurity professionals:
- Understand the roles: Security Engineers, SOC Analysts, Penetration Testers, and AppSec Engineers each require specific skills and experience.
- Go where the talent is: Explore CTF competitions, bug bounty platforms, security conferences, and open-source projects to connect with skilled candidates.
- Streamline hiring: Simplify job requirements, offer competitive salaries (e.g., $124,910 average for Security Engineers), and accelerate hiring timelines to 3–4 weeks.
- Retain talent: Provide career growth opportunities, flexible work arrangements, and a supportive team culture.
Cybersecurity hiring demands a focused, trust-driven approach. Skip generic job boards and build relationships in specialized communities to find the right talent quickly.
Cybersecurity Role Types Explained
With the ongoing talent gap in cybersecurity, clearly defining role types is essential for aligning hiring strategies with job needs. Cybersecurity roles differ significantly in their focus, required skills, and career trajectories.
Security Engineer vs. Penetration Tester
Security Engineers are the architects of defense. They design and automate security infrastructures such as firewalls, endpoint detection and response (EDR) systems, encryption protocols, and workflows. Proficiency in programming languages like Python, Go, or Rust is crucial for automating defenses and creating threat detection rules .
Penetration Testers, on the other hand, are ethical hackers. Their job is to think like attackers, conducting authorized tests to identify vulnerabilities before they can be exploited. By simulating attacks, they expose weaknesses, document findings, and recommend solutions . The mindset difference between these roles is striking: security engineers ask, "How do I make this system secure?" while penetration testers ask, "How can I break into this system?" .
"If SOC analysts are the pilots, security engineers built the aircraft." - Unihackers
When hiring Security Engineers, seek candidates with 4–6 years of prior IT or development experience, as direct entry into these roles is uncommon . For Penetration Testers, certifications like OSCP or CEH are strong indicators of hands-on expertise . In the U.S., security engineers earn an average salary of about $124,910, with senior engineers at top tech firms earning upwards of $250,000 in total compensation . Matching candidates’ skills to the specific demands of each role is key to successful recruitment in cybersecurity. Utilizing the right developer sourcing tools can further streamline this process.
Next, let’s look at roles that focus on both reactive and proactive approaches to security.
SOC Analyst and AppSec Engineer Roles
Cybersecurity teams also depend on specialists who handle real-time monitoring and secure application development.
SOC Analysts (Security Operations Center) are the first responders of cybersecurity. They monitor networks around the clock, triage alerts, and investigate suspicious activities. Their work is reactive and often involves high-pressure situations, such as responding to live threats. Many SOC analysts work in 24/7 shifts, and entry-level positions typically pay between $50,000 and $100,000, making this a common starting point for cybersecurity careers .
AppSec Engineers (Application Security Engineers) focus on securing the software development lifecycle. They conduct code reviews, design secure systems, and integrate security measures into development processes. Unlike SOC analysts, their work is proactive and project-oriented, requiring strong programming skills in languages like Python or Java . These roles often demand 3–6 years of IT or development experience and offer salaries ranging from $110,000 to $175,000 .
The primary distinction here lies in their focus: SOC analysts concentrate on detecting and responding to active threats, while AppSec engineers work to prevent vulnerabilities before software is deployed. When hiring SOC analysts, look for candidates with the ability to remain calm under pressure - technical skills can be taught, but a composed mindset during stressful situations is invaluable . Aligning candidates’ strengths with the unique demands of these roles ensures a more effective cybersecurity team.
Where to Find Cybersecurity Candidates
Traditional job boards often fall short when it comes to sourcing top-tier cybersecurity talent. The best professionals in this field tend to focus on solving real-world problems and engaging in active projects rather than polishing resumes or browsing job listings. To connect with them, you need to meet them where they already spend their time.
CTF Competitions and Communities
One effective way to find skilled cybersecurity professionals is by tapping into Capture the Flag (CTF) competitions. These are hands-on hacking challenges that test participants in areas like web exploitation, cryptography, reverse engineering, and forensics. Platforms such as Hack The Box, TryHackMe, and CyberTalents are hubs where talented individuals showcase their skills in practical scenarios.
CTFs not only highlight technical expertise but also reveal a candidate's ability to solve problems under pressure and communicate complex solutions clearly. Websites like CTFtime.org track top-performing teams and individuals, offering a way to identify standout talent. Reviewing write-ups from participants can give you deeper insight into their technical depth and thought processes.
Different CTF formats can help identify specific skill sets. For example:
- Jeopardy-style CTFs: Focus on isolated challenges, ideal for assessing generalists or junior-to-mid-level talent.
- Attack-defense CTFs: Simulate real-time incident response, a great way to evaluate senior engineers or SOC analysts.
"Hiring cybersecurity talent is hard, and traditional interviews rarely reflect real-world ability. The process is time-consuming, unreliable, and often a gamble."
– Ning Wang, CEO, OffSec
Bug Bounty Platforms
Bug bounty platforms are another excellent source of cybersecurity talent. These platforms connect you with ethical hackers who specialize in identifying vulnerabilities that automated tools often miss. HackerOne and Bugcrowd are two leading platforms in this space. In 2025, HackerOne reported a 210% rise in AI-related vulnerability reports, with one critical vulnerability being discovered every hour .
Both platforms rank researchers on leaderboards based on the severity and volume of vulnerabilities they uncover. Monitoring these leaderboards provides access to highly skilled, passive talent. For instance, Motorola Mobility saved an estimated $60 million in potential breach costs by partnering with ethical hackers through Bugcrowd .
"The hacker community can outrun threat actors at an unprecedented pace. Not even the largest security teams can do what Bugcrowd can achieve."
– Ross McKerchar, CISO, Sophos
Security Conferences and Meetups
Industry events like DEF CON, Google CTF, and HITCON are prime networking opportunities for connecting with elite cybersecurity professionals. These gatherings attract individuals who are deeply passionate about their craft, often investing their own time and resources to attend. Finalists from major competitions at these events often represent the top talent globally.
Regional conferences and local meetups are also valuable for discovering mid-level and emerging professionals. These settings encourage candid networking and provide opportunities to observe potential hires in action through workshops. Some companies even host their own CTFs at these events to assess candidates in real-time .
Open Source Security Projects
Open-source platforms like GitHub are treasure troves for finding talent. By reviewing contributions to security tools and projects, you can assess a candidate's coding standards, teamwork, and genuine interest in advancing the field.
For example, OffSec's Talent Finder connects employers with professionals who have earned rigorous certifications like OSCP, OSCE³, or OSED. These certifications require candidates to demonstrate real-world exploitation skills in timed, practical exams, offering a more reliable measure of ability than traditional interviews.
Contributions to open-source projects also highlight a candidate's dedication to the security community. Whether they maintain tools, write documentation, or contribute to projects like Metasploit or OWASP, their active involvement reflects both technical expertise and a collaborative mindset - qualities essential for thriving in team environments.
How to Evaluate Cybersecurity Candidates
Evaluating cybersecurity candidates isn't just about finding the right people - it's about making sure they can actually do the job. While many organizations lean on skills-based assessments to narrow down their options , the challenge lies in designing tests that measure real problem-solving skills instead of rote memorization.
Creating Practical Technical Tests
Once you've sourced candidates - especially from unconventional paths - the next critical step is assessing their abilities in realistic scenarios. The most effective technical tests mimic what a typical workday might look like. For entry-level roles, focus on core tasks like malware analysis, risk assessment, and basic penetration testing. For junior-level candidates, introduce more advanced challenges, such as cloud security, incident response, and digital forensics .
The goal here is to understand how candidates think, not just what they know. For example, you could present a scenario involving a compromised production database. Ask the candidate to outline their top five actions and identify the key stakeholders they'd involve. This kind of test gives insight into their logical reasoning and ability to prioritize tasks under pressure.
Certifications That Matter
Certifications can help verify a candidate’s baseline knowledge, but not all credentials are created equal. For entry-level positions, certifications like ISC2's Certified in Cybersecurity (CC) and CompTIA's Security+ are solid benchmarks . These credentials confirm foundational skills without requiring years of professional experience.
However, requiring advanced certifications for entry-level roles can be counterproductive. For instance, 34% of employers require CISSP certification for entry-level jobs, even though it demands five years of experience . This creates unnecessary hurdles that may push qualified candidates away. While CISSP is respected for advanced roles - its pass rate of 20% to 50% reflects its difficulty - it’s not practical for those just starting out. For junior roles, prioritize certifications that align with the skills candidates can realistically develop early in their careers.
"This gap in what security managers require from early-career talent versus what these groups can realistically achieve creates a significant barrier to entry." - ISC2 2025 Cybersecurity Hiring Trends Report
Beyond certifications, a candidate’s ability to communicate and solve problems is just as crucial.
Communication and Problem-Solving Skills
In cybersecurity, technical expertise alone doesn’t cut it. Professionals need to explain vulnerabilities and risks to non-technical stakeholders, like a CFO, in a way that’s clear and actionable. Soft skills such as teamwork, analytical thinking, and clear communication are increasingly valued by hiring managers .
Interviews are the perfect opportunity to evaluate these skills. Have candidates present technical findings in plain language, ensuring they can translate complex issues into terms anyone can understand. Observe how they handle executive-level questions - can they stay calm and think on their feet during a high-stakes discussion? These communication abilities complement technical assessments, providing a more complete picture of the candidate.
Behavioral questions are another great way to assess problem-solving in real-world scenarios. For example, ask, "Can you describe a time when you had to persuade a development team to adopt a new security practice?" or "How did you communicate a risk to senior leadership without causing unnecessary alarm?" These questions shed light on how candidates navigate the human side of cybersecurity, including collaboration, trust-building, and ethical decision-making under pressure .
"Technical skills get them in the door but communication keeps them in the role." - KORE1
Compensation and Keeping Security Talent
::: @figure 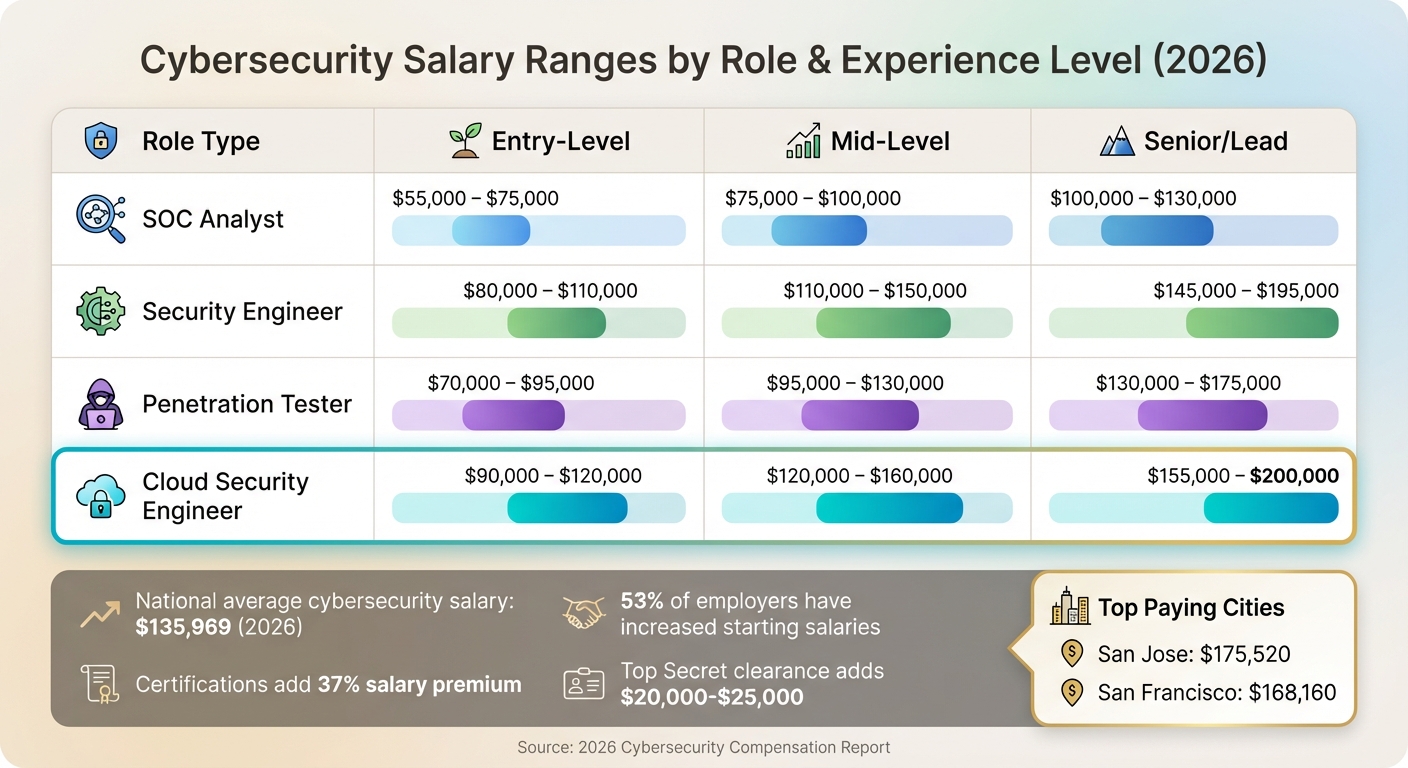 {Cybersecurity Role Salary Ranges by Experience Level 2026}
{Cybersecurity Role Salary Ranges by Experience Level 2026}
Salary Ranges for Security Roles
Cybersecurity professionals are among the highest-paid in tech, with the national average salary hitting $135,969 in 2026. To stay competitive, 53% of employers have increased starting salaries for these roles . While pay varies by position and experience, security roles generally surpass many other tech jobs, such as general engineering and data analysis, in terms of compensation .
For early-career professionals, software engineering salaries often range from $80,000 to $110,000, compared to $55,000 to $80,000 for entry-level security roles. However, by mid-career, both fields align at $120,000 to $160,000 . Specialized positions, such as Cloud Security Engineers, command even higher pay, ranging from $130,000 to $175,000 at mid-to-senior levels. This reflects a critical talent shortage, as noted by 36% of organizations . Similarly, emerging AI Security roles offer a 10% to 20% salary premium over comparable non-AI jobs .
| Role Type | Entry-Level | Mid-Level | Senior/Lead |
|---|---|---|---|
| SOC Analyst | $55,000 – $75,000 | $75,000 – $100,000 | $100,000 – $130,000 |
| Security Engineer | $80,000 – $110,000 | $110,000 – $150,000 | $145,000 – $195,000 |
| Penetration Tester | $70,000 – $95,000 | $95,000 – $130,000 | $130,000 – $175,000 |
| Cloud Security Engineer | $90,000 – $120,000 | $120,000 – $160,000 | $155,000 – $200,000 |
Location also plays a big role in pay. San Jose leads the pack with an average annual salary of $175,520, followed by San Francisco at $168,160 . Certifications are another key factor, with professionals holding relevant credentials earning 37% more than their non-certified peers . For government or defense roles, having Top Secret clearance can add $20,000 to $25,000 to a candidate's pay .
While base salaries are crucial, companies must also focus on total compensation and benefits to attract and retain top talent.
Benefits Security Professionals Value
Competitive pay is just the starting point. Benefits and work flexibility often make or break the deal for cybersecurity professionals. Many engineers value perks like conference passes, certification reimbursements, and dedicated training budgets. Covering high-cost certifications, such as SANS courses (priced between $7,000 and $9,000), shows a company’s commitment to employee growth .
Flexible work arrangements are another major draw. With 48% of cybersecurity professionals feeling exhausted by the constant threat landscape and 47% overwhelmed by their workload , remote work and flexible schedules help alleviate burnout. Beyond flexibility, team quality (78%) and effective leadership (73%) rank as the top retention factors, even above salary or company reputation .
Creating a Team Culture That Retains Talent
While pay and benefits attract talent, a supportive team culture ensures they stay. Retention rates drop notably after the first year, with only 66% of professionals remaining after two years . Clear career paths and skill development opportunities are essential, as 65% of early-career professionals say they would stay at a company for four or more years if they had consistent chances to grow .
Offering professional development during work hours is a strong retention strategy, with 91% of organizations now providing such opportunities . Defining advancement paths - whether in technical expertise, management, architecture, or risk advisory - helps employees see a future with the company . Mentorship programs also play a key role, though 50% of organizations struggle with staff availability for mentoring .
"The strongest satisfaction drivers are teams (78%) and direct managers (73%). Not compensation. Not company brand. The people they work with and the person they report to." - Tom Kenaley, Senior Partner and President, KORE1
Empowering employees with autonomy to manage projects and innovate is another way to keep them engaged and motivated . Fair workload distribution, transparent communication, and regular recognition also go a long way in preventing burnout. With 58% of hiring managers worried about losing entry- and junior-level team members , creating a culture that emphasizes growth, balance, and trust is essential - especially given the staggering 3.5 million cybersecurity talent gap that continues to challenge recruitment efforts.
Building Trust in Your Recruitment Process
Mistakes to Avoid in Candidate Outreach
Cybersecurity professionals are naturally attuned to spotting red flags. Their entire careers revolve around identifying risks, analyzing vulnerabilities, and dismantling weak claims. So, when your outreach includes unnecessary personal details or feels intrusive, you've already lost their trust. Security engineers scrutinize your messages just as they would audit a third-party system - looking for flaws and questioning how you accessed their information.
Cold messages filled with excessive personal details scream poor respect for privacy and sloppy data practices. It's an immediate turn-off. Similarly, generic, automated templates do more harm than good. Dan Houser, 2024 Board of Directors Chair at ISC2, highlights this challenge:
"Staffing is becoming increasingly challenging as recruiters are slammed with AI-polished resumes delivered via automation... With so much noise, how do we ensure true professionals are finding roles?"
From the candidate's perspective, this "noise" translates into countless identical InMails and impersonal pitches that fail to show any understanding of their work or values.
Avoid buzzwords and vague promises - they won’t cut it with security professionals who expect credibility backed by evidence. For instance, requiring a CISSP certification for an entry-level role or failing to distinguish between "required" and "desired" qualifications can alienate the very candidates you're trying to attract. These missteps create unnecessary barriers and reinforce skepticism about unrealistic expectations .
To succeed in infosec recruiting, respectful and transparent communication is key. Missteps in outreach only deepen mistrust, making personal connections and opt-in channels essential for building relationships with security professionals.
Using Warm Introductions and Opt-In Methods
Cold, impersonal messages don’t work with security talent - warm introductions are the way to go. The best security engineers aren’t hunting for jobs on boards. As Tom Kenaley, Senior Partner and President at KORE1, puts it:
"These candidates get recruited through relationships, not job posts"
Building credibility starts with leveraging your network. Referrals, community connections, and peer recommendations are far more effective than generic outreach.
Opt-in platforms also play a crucial role. These are spaces where professionals have chosen to be visible, ensuring privacy and signaling genuine openness to opportunities. For example, Dice offers access to 3.6 million tech profiles, 99% of which include resumes and verified contact details - indicating these professionals want to be contacted . Similarly, daily.dev Recruiter uses a double opt-in model, where developers actively indicate their interest in new roles. This ensures every introduction feels personal, contextual, and respectful - never spammy.
This approach aligns perfectly with the values of security engineers, who prioritize transparency and control. By using warm introductions and opt-in methods, you can create meaningful connections without compromising trust.
Conclusion
Key Takeaways for InfoSec Recruiting
Recruiting cybersecurity engineers requires a tailored approach that differs significantly from general software hiring. The global shortage of cybersecurity talent underscores the need to align hiring strategies with how InfoSec professionals operate.
Use specialized sourcing channels. Cybersecurity experts often gather in CTF (Capture The Flag) communities, participate in bug bounty programs, or contribute to open-source security projects. These are the spaces to focus on - not traditional job boards. When reaching out, prioritize privacy and demonstrate technical knowledge to build trust. As ISC2 leadership highlights, certifications are still key differentiators . Look for hands-on experience and certifications like Security+ or CISSP instead of relying solely on degrees in computer science.
Speed and transparency matter. The average time to fill a security role is 3–6 months, but top companies manage to hire within 3–4 weeks by pre-approving budgets and simplifying interview processes . Avoid setting unrealistic expectations, such as requiring a CISSP certification for entry-level roles. In fact, 90% of hiring managers are open to candidates with practical experience and entry-level certifications over those who only hold a degree .
Retention starts on Day One. Team and manager quality account for 78% and 73% of employee satisfaction, respectively. To prevent burnout, invest in professional development opportunities and establish clear career paths . Respect privacy and technical expertise in every interaction to build long-term trust.
Getting Started with Your Security Hiring
To put these strategies into action, focus on connecting with pre-qualified cybersecurity professionals through opt-in platforms. For example, daily.dev Recruiter uses a double opt-in model, ensuring that every interaction is warm, respectful, and contextually relevant - exactly what security engineers expect. This means no cold-messaging or relying on outdated profiles, but instead engaging with active professionals who are genuinely interested in new opportunities.
Refine your job descriptions to emphasize must-have skills, provide accurate compensation data, and include practical technical assessments. With 88% of organizations reporting security incidents linked to skills shortages, leaving roles unfilled comes at a much higher cost than investing in a trust-driven, efficient hiring process .
FAQs
Which cybersecurity role should I hire first?
Hiring entry- or junior-level professionals can be a smart way to tackle the cybersecurity talent shortage. By focusing on these roles, you create opportunities to train and mentor new team members, laying the groundwork for long-term growth. This approach also opens doors to candidates from diverse or non-traditional backgrounds, expanding your talent pool. Plus, it helps avoid the fierce competition over seasoned experts, offering a more sustainable path to building a strong cybersecurity team in today’s challenging job market.
Where can I find cybersecurity engineers outside job boards?
To discover cybersecurity engineers outside of traditional job boards, consider Capture the Flag (CTF) competitions and cybersecurity platforms. Hosting or sponsoring CTF events is a great way to evaluate practical skills while building a network of potential candidates. Similarly, platforms offering hands-on challenges can connect you with professionals who have proven expertise. Another effective approach is engaging with cybersecurity communities and attending conferences, where you can meet highly skilled individuals who might not be actively searching for jobs but are well-qualified.
What should a cybersecurity technical test include?
A cybersecurity technical test should measure practical, job-specific skills. This means focusing on tasks like penetration testing, code review, or identifying and analyzing vulnerabilities in IT systems. The emphasis should be on hands-on activities that mirror actual work scenarios, such as evaluating attack surfaces, testing the effectiveness of security controls, or working with SIEM tools to analyze data.
Skip theoretical questions - they don't provide much insight into someone's ability to handle real-world challenges. Instead, create a simulated environment that tests both technical know-how and problem-solving skills under realistic conditions. This approach gives a much clearer picture of a candidate's readiness for the role.


.png)