Hiring cybersecurity professionals in 2026 is challenging, with 4.8 million unfilled roles globally and 500,000–700,000 vacancies in the U.S. alone. Companies face risks like $1.76 million higher breach costs due to understaffed teams, while 88% of organizations link major incidents to skill shortages. Tight budgets and lengthy hiring processes further complicate recruitment.
Key takeaways:
- Role clarity matters: Define roles like Security Engineer, SOC Analyst, or Penetration Tester to attract the right talent. Avoid unrealistic "unicorn" job descriptions.
- Sourcing strategies: Use platforms like Hack The Box, HackerOne, and events like DEF CON to find skilled professionals. Trust-based networks are critical for roles requiring security clearances.
- Candidate evaluation: Focus on practical tests, scenario-based questions, and communication skills. Avoid excessive unpaid assignments or unclear hiring processes.
- Compensation insights: Salaries range from $70,000 to $230,000, with premiums for AI/ML expertise, cloud security, and security clearances. Benefits like training budgets, remote work, and clear advancement paths attract top talent.
To close the talent gap, organizations must streamline hiring, offer competitive pay, and create supportive work environments. Up next: actionable tips to source, evaluate, and retain cybersecurity experts.
Cybersecurity Role Types: Matching Skills to Your Needs
Security Engineer vs. Penetration Tester vs. SOC Analyst vs. AppSec Engineer
Cybersecurity is a field with distinct roles, each requiring unique expertise. For instance, Security Engineers focus on building and maintaining protective systems like firewalls, encryption tools, and automated security measures .
SOC Analysts are the first line of defense, responsible for monitoring systems, analyzing network logs, prioritizing alerts, and investigating suspicious activities in real time . Salary ranges reflect their experience: entry-level SOC Analysts typically earn between $70,000 and $110,000, while Security Engineers with three to five years of experience can command $110,000 to $165,000 .
Penetration Testers, often referred to as ethical hackers or Red Teamers, simulate attacks to uncover vulnerabilities before they can be exploited. Their salaries range from $105,000 to $160,000 . On the other hand, Application Security (AppSec) Engineers focus on securing software by analyzing code for weaknesses and teaching developers about secure coding practices. These roles are among the highest-paid in cybersecurity, with earnings between $140,000 and $230,000 .
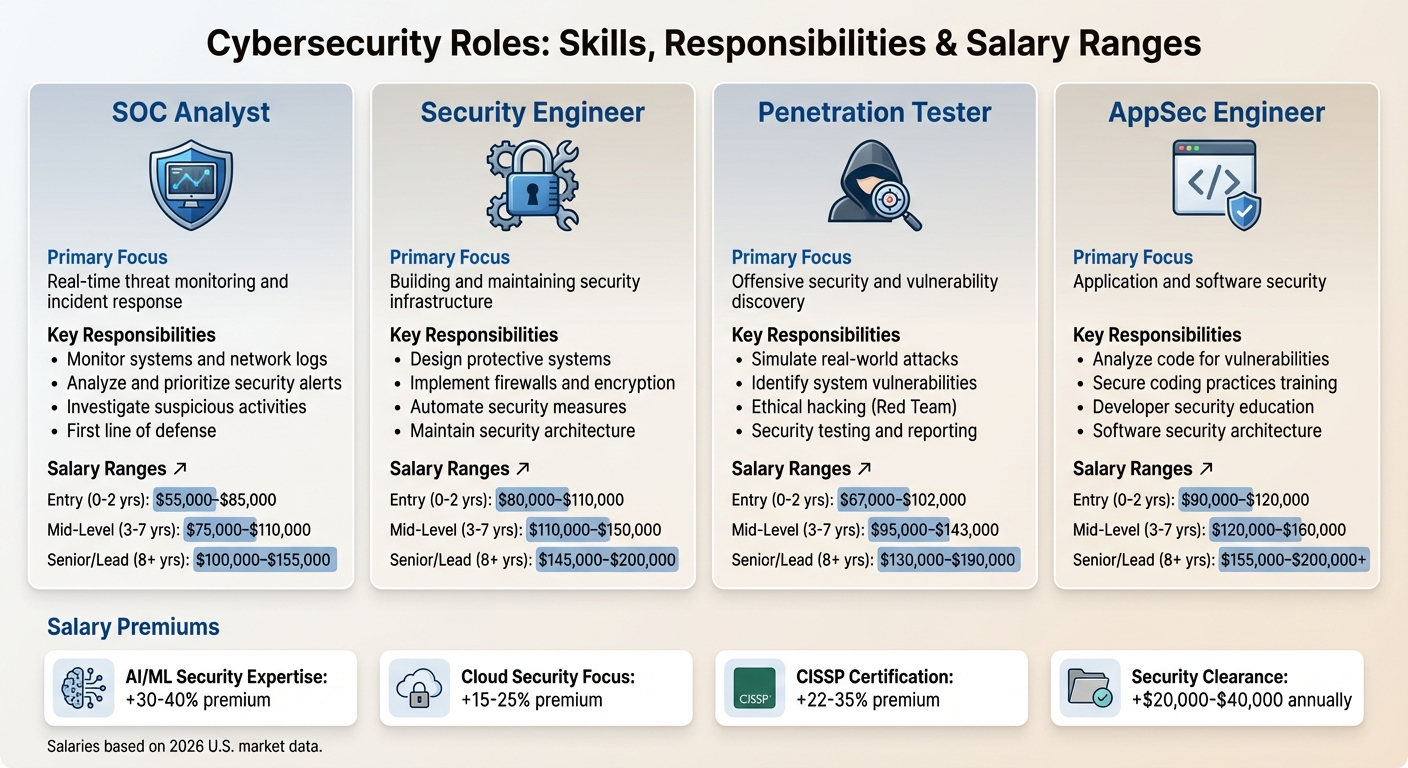
The variations in salaries reflect both the level of specialization and demand in the market. For example, professionals with AI/ML expertise earn a premium of 30%–40%, while those holding CISSP certifications can see a pay boost of 22%–35% .
Having clear distinctions among these roles helps organizations better understand responsibilities and simplifies the hiring process by utilizing the right developer sourcing channels.
Why Clear Role Definitions Lead to Better Hires
As the above roles demonstrate, defining job responsibilities clearly is essential for finding the right talent. Vague job descriptions can lead to mismatched hires. Implementing proactive sourcing strategies can help mitigate these risks. For example, asking for a "cybersecurity professional" who can design infrastructure, monitor threats, perform penetration tests, and handle compliance is unrealistic. As KORE1 aptly stated, "Hiring the wrong type is like calling a dermatologist when you need an orthopedic surgeon" .
Well-defined roles bring two major advantages. First, they attract candidates with the specific skills needed for the job instead of generalists who may lack depth in critical areas. Second, they speed up the hiring process. While filling a cybersecurity position typically takes three to six months, dragging the process beyond three or four weeks can result in losing top candidates to faster-moving employers .
Avoid the "unicorn trap" of setting impossible requirements, like demanding 10 years of experience in technologies that have existed for only five years or requiring every major certification (CISSP, CISM, CEH) for a mid-level salary. These unrealistic expectations can deter qualified candidates who meet most of the actual needs. The reality is that 90% of cybersecurity teams report significant skills gaps even when they are "fully staffed." The problem isn't the number of hires - it's ensuring the right specialists are in the right roles .
Why Traditional Sourcing Fails for Security Professionals
Clearance Requirements and Trust Issues
Hiring security professionals, particularly for government or defense roles, operates in a completely different realm than standard IT recruitment. As KORE1 describes, security clearances create a "separate market" with unique challenges. For example, cleared candidates often earn $20,000 to $40,000 more annually than their non-cleared counterparts with the same technical expertise . However, platforms like LinkedIn and Indeed don't offer the detailed filters needed to identify candidates with these clearances .
This lack of visibility forces recruiters to rely on slower, manual processes. Instead of resume databases, they turn to trusted professional networks where reputations and credentials are already verified within the community . This trust-based approach is essential but time-consuming.
Speed is another issue. While it typically takes three to six months to fill a cybersecurity position, top cleared candidates are often snapped up by competitors in just three to four weeks. Defense contractors have upped the stakes, offering much higher salaries to secure this rare talent pool . These challenges highlight the need for better developer sourcing tools to connect with and engage security professionals.
How Bad Outreach Drives Candidates Away
Clearance challenges aside, poor outreach methods can also alienate top security talent. By nature, security professionals are highly protective of their personal data. If outreach efforts feel invasive or misuse personal information, recruiters are often dismissed outright . As Steven Lu from Pin explains, "Cybersecurity professionals value privacy... recruiters who can write precise searches on tech-specific platforms fill roles faster" .
Generic outreach messages add to the problem. Many of these specialists are already overwhelmed by demanding workloads, and the flood of identical, impersonal messages on platforms like LinkedIn only makes things worse . These InMails are often ignored or lost in the shuffle.
To make matters more complicated, the most qualified professionals are typically passive candidates - deeply focused on their current roles rather than actively seeking new opportunities . The stakes for ineffective sourcing are high: firms with understaffed security teams experience breach costs that are, on average, $1.76 million higher than those with fully staffed teams .
Where to Find Cybersecurity Talent
Closing the cybersecurity talent gap means exploring creative ways to connect with skilled professionals. By tapping into platforms and events where candidates actively demonstrate their expertise, you can find talent that stands out.
CTF Competitions and Bug Bounty Platforms
Capture The Flag (CTF) competitions and bug bounty platforms are goldmines for discovering cybersecurity talent. These platforms give you a front-row seat to watch professionals in action, solving real-world challenges. Unlike resumes, which often rely on listing certifications and past roles, these tools let you see candidates’ skills firsthand.
Take Hack The Box, for example. It’s home to over 4.3 million security enthusiasts, with more than 938,000 users open to recruiter outreach . Participants showcase their abilities in areas like cryptography, cloud security, and reverse engineering. You can even filter candidates by rank and review their performance on specific challenges.
Similarly, bug bounty platforms like HackerOne and Bugcrowd act as live portfolios for ethical hackers. HackerOne has paid out over $380 million in bounties through more than 1,000 active programs . By monitoring public disclosures (called "Hacktivity" on HackerOne), you can identify researchers who’ve uncovered critical vulnerabilities and written detailed, professional reports - demonstrating both technical expertise and communication skills.
"One customer, one of their tier-one analysts, came in first place and beat out all of their tier-three analysts. That person got promoted to SOC manager and ended up being their leader in their environment."
Real-world examples highlight how effective these platforms can be. At Splunk’s 10th annual "Boss of the SOC" CTF in September 2025, a tier-one analyst outperformed tier-three analysts and earned a promotion to SOC manager. Another participant, Katie Brown, was recruited and later became Director of Platform Security .
You can also host branded challenges on platforms like Hack The Box. By submitting custom virtual machines or "Fortress Labs", you can test candidates in controlled scenarios, offering a practical way to evaluate their problem-solving skills while respecting their time.
Security Conferences and Industry Events
Beyond online platforms, security conferences like DEF CON and Black Hat provide face-to-face opportunities to engage with top talent. These events attract professionals eager to tackle emerging threats - exactly the mindset you want on your team.
Many conferences include CTF competitions, where you can observe candidates under pressure. Watching how they collaborate, manage time, and communicate technical findings offers valuable insight into their abilities. According to Hack The Box research, over 70% of managers view team-based events like CTFs as effective for identifying talent and boosting engagement .
Approaching conference attendees requires a thoughtful touch. These professionals are there to learn and network, not to endure generic job pitches. Start conversations about their interests, the talks they enjoyed, or the challenges they’ve faced. Building genuine connections goes a long way and complements the digital sourcing strategies discussed next.
Online Communities and Professional Networks
Cybersecurity professionals often gather in specialized forums and professional networks to share insights, discuss threats, and collaborate on solutions. These spaces thrive on trust and reputation, making them far more effective than generic job boards for finding skilled candidates.
Platforms like CyberTalents blend CTF-based skill assessments with job opportunities, creating an environment where professionals engage with technical content while staying open to career moves . Unlike LinkedIn, these platforms prioritize technical skills over networking.
Vulnerability Disclosure Programs (VDPs) on platforms like HackerOne also serve as talent pools for up-and-coming security researchers. While not all VDPs offer bounties, they attract individuals eager to build their reputations and advance their careers .
"Every organization has blind spots. Having the hacker community on the other side of the screen looking at those things you've missed means you can close those holes."
When reaching out to candidates in these forums, it’s essential to show that you’ve done your homework. Security professionals are highly aware of how their data is used, and generic outreach won’t cut it. Reference their specific work, challenges they’ve solved, or community contributions. Demonstrating genuine interest in their expertise will make your outreach far more effective.
How to Assess Cybersecurity Candidates
Once you've found promising candidates through CTF competitions, bug bounty platforms, or industry events, the next step is evaluating them thoroughly to ensure you're hiring the right cybersecurity professionals. A robust assessment process helps identify genuine expertise and filters out those who might not meet the demands of the role.
Technical Skills Tests and Practical Scenarios
Georgina Day, Head of Cybersecurity Recruitment at Leap29, stresses the importance of using technical tests that mirror real-world challenges .
Start with tests that cover core concepts like the CIA triad, encryption, network protocols, and intrusion detection/prevention systems (IDS/IPS). Include practical exercises involving tools such as Wireshark, Nmap, and Splunk . For roles in Security Engineering or DevSecOps, you can ask candidates to write Python scripts for log parsing or use Bash to automate forensic searches . Another effective tactic is presenting insecure code snippets and asking candidates to identify and fix vulnerabilities, which helps gauge their hands-on security coding skills .
Scenario-based challenges are particularly useful for evaluating how candidates handle pressure. For example, you could ask, "If you suspect a ransomware attack has started, what is your immediate response?" This type of question reveals how they prioritize actions and solve complex problems . For compliance-focused roles, case studies can be a great tool. Ask candidates to draft risk assessments, pinpoint policy gaps, or align controls with frameworks like ISO 27001, NIST, or GDPR .
"Don't just prepare for WHAT you know -- prepare to explain WHY you chose that method, tool, or response."
Day highlights the importance of understanding the reasoning behind decisions. Candidates who can explain their choices demonstrate the ability to adapt their knowledge to your organization's unique challenges, rather than relying solely on rote memorization.
After confirming technical skills, shift your focus to how well candidates communicate and work with others, especially under pressure.
Communication and Team Collaboration Skills
Strong communication is essential in cybersecurity. Candidates should be able to explain technical risks in a way that makes sense to both technical teams and non-technical executives .
Human error is a leading cause of security breaches, so the best candidates understand that security is as much about people as it is about technology . Samidha Thote, a UX Design Specialist, notes:
"Assuming every user to adhere to the security controls without making an error at all times, would prove to be an ineffective solution."
When assessing candidates, pay attention to how they design solutions that account for real-world user behavior. Do they create controls that align with how people actually work, or do they expect perfect compliance? With 31.9% of IT security professionals ignoring threat alerts due to alert fatigue , candidates who can manage large data volumes and prevent alarm overload bring a practical mindset to the table.
Assessment Mistakes That Lose Good Candidates
Even with the best evaluation methods, certain mistakes can drive away top-tier cybersecurity talent.
One common error is rushing the process. While the shortage of cybersecurity professionals might tempt you to move quickly, Iceberg warns:
"In an industry where a single mistake can lead to significant breaches, identifying warning signs during interviews is your first line of defense against poor hiring decisions."
However, being thorough doesn't mean dragging candidates through a marathon of interviews. Strike a balance to keep the process efficient yet comprehensive .
Excessive unpaid assignments are another red flag. Limit assessments to 1–2 hours, or offer compensation for longer tasks . If you're concerned about intellectual property, have candidates sign agreements ensuring their solutions won't be used unless they're hired .
Privacy-invasive screening can also alienate candidates. Avoid requesting unnecessary personal details or conducting intrusive background checks before extending an offer. Similarly, unclear job descriptions filled with jargon can signal that you don't fully understand the role's requirements .
Excluding your technical team from interviews is a missed opportunity. Security specialists can catch subtle inconsistencies that others might overlook. Involve them in the process, but avoid overwhelming candidates with an endless series of group interviews, which can come across as disorganized .
Lastly, offering salaries below industry standards is a quick way to lose candidates. As Career Contessa puts it:
"The interview is for you. It's not a pageant or a contest. There needs to be a mutual buy-in for you and the organization."
Be transparent about compensation, work culture, and timelines. Building trust is essential when hiring cybersecurity professionals.
Cybersecurity Engineer Compensation and Benefits
Salary Ranges and Security Role Premiums
Cybersecurity professionals often earn higher salaries than software engineers, with specialization further boosting earnings. By 2026, the average U.S. cybersecurity salary is expected to reach $135,969, while a Cybersecurity Engineer's total compensation averages $200,797, including $33,946 in additional cash bonuses. In contrast, software engineers average $139,723 annually.
The gap widens at mid-to-senior levels, especially in specialized fields. Experts in AI and ML security can earn 30% to 40% more than those in traditional roles due to limited talent availability. Similarly, cloud security roles offer a 15% to 25% premium over on-premises-focused positions. Security clearance requirements create another pay tier; for instance, a Full Scope Polygraph clearance can add $45,000 to $65,000 annually, translating to up to $1.3 million in additional lifetime earnings.
| Role | Entry (0-2 yrs) | Mid-Level (3-7 yrs) | Senior/Lead (8+ yrs) |
|---|---|---|---|
| SOC Analyst | $55,000–$85,000 | $75,000–$110,000 | $100,000–$155,000 |
| Security Engineer | $80,000–$110,000 | $110,000–$150,000 | $145,000–$200,000 |
| Penetration Tester | $67,000–$102,000 | $95,000–$143,000 | $130,000–$190,000 |
| AppSec Engineer | $90,000–$120,000 | $120,000–$160,000 | $155,000–$200,000+ |
Location also plays a significant role in pay. For example, San Jose-Sunnyvale-Santa Clara tops the list with an average salary of $175,520, followed by San Francisco-Oakland-Hayward at $168,160, Seattle-Tacoma-Bellevue at $152,660, and Washington-Arlington-Alexandria at $138,410. Salaries in cybersecurity are growing at an annual rate of 7% to 10%. Certifications like CISSP can boost earnings by 22% to 35%, making them a solid investment for professionals.
While these numbers highlight the financial rewards of cybersecurity roles, benefits and incentives are equally important in retaining top talent. Competitive salaries set the stage, but additional perks often make the difference in attracting and keeping skilled professionals.
Benefits That Attract Security Professionals
In addition to competitive pay, cybersecurity professionals seek benefits that support their growth and well-being. Training budgets are a key factor - with SANS courses costing upwards of $8,000, companies that fund employee training see better retention rates. Offering reimbursement for certifications like CISSP ($749) or OSCP ($1,499–$1,749) demonstrates a commitment to professional development. Defense contractors frequently offer $10,000 to $15,000 annually in tuition assistance.
Remote work is another highly valued benefit, especially for commercial and GRC roles, though positions requiring SCIF access often remain on-site. Signing bonuses, typically ranging from $5,000 to $20,000, and relocation packages worth $10,000 to $30,000, also enhance a job offer's appeal for candidates open to moving. Providing budgets for conference attendance supports ongoing education, which is crucial given that 48% of security professionals report burnout from the constant threat landscape.
Clear career advancement opportunities are another major draw, with nearly one-third of professionals ranking this as a top priority. Leadership quality also plays a crucial role in retention, with 73% of professionals influenced by their direct manager and 78% by their team. For organizations unable to match top-tier salaries - a challenge cited by 33% of companies - strong mentorship programs and knowledge-sharing initiatives can help bridge the gap. These efforts contribute to job satisfaction, currently reported at 68% among security professionals.
Building a Security Team Culture That Retains Talent
Mentorship Programs and Knowledge Sharing
Structured mentorship can be a game-changer for team development and retention. The "Build, Break, Fix, Teach" model is particularly effective - teaching not only strengthens individual expertise but also enhances team-wide knowledge. Pairing junior team members with experienced professionals creates clear growth opportunities and fosters loyalty over time.
Great security leaders act as mentors and coaches. A Google study revealed that employees value leaders who genuinely care about their lives and careers and prioritize regular one-on-one meetings. This leadership style is crucial, especially since 66% of cybersecurity professionals report significantly higher levels of occupational stress compared to five years ago. Hands-on training methods, like tabletop exercises and cyber ranges, provide engaging, collaborative learning experiences while improving critical skills.
These mentorship and knowledge-sharing efforts lay the groundwork for career growth and continuous learning.
Career Advancement Paths and Skill Development
While mentorship is important, offering clear career advancement paths is equally vital for retaining top talent. Transparent growth roadmaps that outline necessary skills and milestones help employees see their future within the organization. With 47% of tech professionals expected to actively seek new roles in 2025 - up from 29% the previous year - the absence of growth opportunities can lead to losing valuable team members.
Investing in industry-recognized certifications shows employees that their development matters. Providing annual budgets for certifications like CISSP or OSCP, along with dedicated study time, signals a commitment to their professional growth beyond just compensation. Introducing cutting-edge tools - like AI-driven threat detection systems or advanced cloud security platforms - keeps team members engaged with the latest developments in the field. This is especially important as 81% of professionals cite the increasingly complex threat landscape as a major source of workplace stress. Regular opportunities for skill-building not only combat burnout but also keep employees motivated.
A defined career path paired with continuous learning opportunities fosters a forward-thinking and engaged security culture.
Team Environment and Cross-Functional Collaboration
To retain talent, mentorship and career growth must be complemented by a collaborative and inclusive team environment. Security teams thrive when they work across departments rather than in isolation. Embedding security professionals with developers, data scientists, and engineers ensures that security becomes a shared responsibility. Practices like Purple Teaming - where red and blue teams collaborate - help identify and address vulnerabilities effectively. Security ambassador programs that involve representatives from legal, risk management, audit, and IT helpdesk further enhance visibility and create a supportive network across the organization.
Autonomy is another key factor in engagement. High-performing professionals are most motivated when they have the freedom to solve problems creatively and contribute to meaningful projects. By automating repetitive tasks through tools like orchestration platforms, organizations allow their security teams to focus on high-value, challenging work. Flexible work arrangements and respect for work-life balance are also crucial, especially considering that 74% of tech professionals planned to change employers as of February 2026.
A collaborative, supportive environment ensures security teams remain engaged and committed to their mission.
How daily.dev Recruiter Connects You with Security-Minded Developers
Finding the right cybersecurity professionals can be tricky. Traditional recruiting methods often miss the mark because they focus on static resumes that only show past experience. But when you're hiring for infosec roles, you need people who are actively learning, staying updated on the latest threats, and genuinely curious about solving security challenges. That’s where daily.dev Recruiter comes in, offering a fresh approach built on real-time developer insights.
This platform taps into the behavior of over one million developers. Instead of relying on self-reported skills, it identifies talent by analyzing what developers are currently engaging with. For instance, if someone frequently interacts with content about container security, secure JavaScript runtimes, or the latest CVE disclosures, it’s a good sign they’re deeply involved in these areas right now - not just in the past.
Another key feature is its double opt-in process, which ensures respect for developers' privacy. Developers must first agree to be visible to recruiters, and only after mutual consent is an introduction made. This eliminates cold outreach and spam, creating a more respectful and efficient recruiting process.
And it works. As Nimrod Kramer explains:
"We're turning real developer behavior (what people read, follow, and build) into high-signal matches. We help recruiters understand who a developer is now, not just who they were years ago." – Nimrod Kramer
This approach ensures you’re connecting with security professionals who are not just qualified but actively immersed in the field.
FAQs
What’s the fastest way to hire a cybersecurity engineer without sacrificing quality?
Finding and hiring a cybersecurity engineer quickly, without cutting corners, requires a strategic approach. Start by exploring specialized sourcing channels. Look into cybersecurity communities, Capture The Flag (CTF) competitions, bug bounty platforms, and security conferences. These places are teeming with professionals who are actively engaged in the field.
When evaluating candidates, focus on targeted technical assessments. Skip generic questions and instead test for the specific skills that align with the role. By zeroing in on relevant expertise, you can ensure you're bringing on someone who meets your security standards while streamlining the hiring process. Trust and discretion are key throughout this process, especially in such a sensitive field.
How do I choose between a SOC analyst, security engineer, AppSec engineer, and pentester?
When deciding on the right role for your organization, consider your specific needs:
- SOC analysts focus on monitoring networks and responding to threats, making them ideal for real-time threat detection and response.
- Security engineers concentrate on designing and maintaining secure infrastructure, emphasizing proactive defenses to prevent attacks.
- AppSec engineers specialize in securing software through code reviews and testing, which is crucial for teams heavily involved in development.
- Pentesters simulate real-world attacks to uncover vulnerabilities, making them a great fit for organizations prioritizing offensive security measures.
It's common for professionals to begin their careers in SOC roles, gaining hands-on experience with threats, and later transition into engineering positions as they develop skills in automation and infrastructure.
How can I assess cybersecurity candidates without long unpaid take-home tests?
To evaluate cybersecurity candidates effectively, focus on practical tasks and role-specific challenges. Start with concise exercises tailored to the job's key responsibilities to gauge their technical expertise. Incorporate scenario-based interviews to see how they handle pressure and make decisions in real-time situations. Additionally, use behavioral interviews to assess their soft skills, such as communication and teamwork. This method not only respects the candidate's time but also provides a clear picture of their practical capabilities.


.png)